Did you know that a hacker attempts an attack every thirty-nine seconds? This equates to nearly 2,200 incidents daily, leaving many individuals feeling quite vulnerable online. Maintaining safety requires more than just a simple password or a basic firewall nowadays.
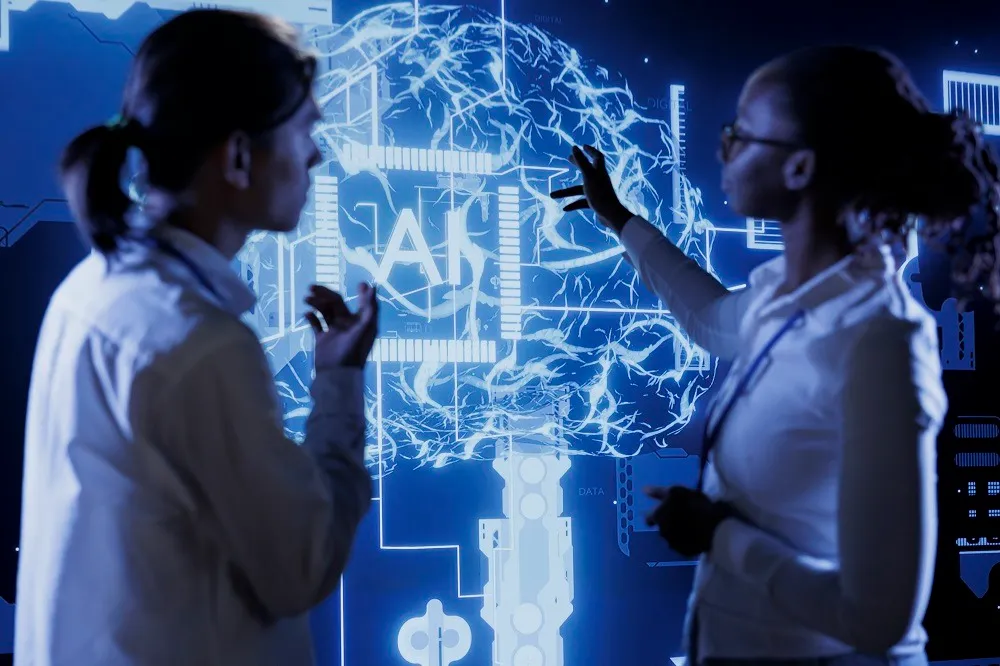
This is exactly how ai improves cybersecurity by acting as a digital guardian that never sleeps. It scans for patterns and stops threats before they cause any real damage to your personal data. Such systems are changing the way we look at digital safety across the globe.
Using ai in cybersecurity helps companies protect sensitive information with incredible speed. These smart tools learn from every interaction, making our internet experience much safer and more reliable for everyone. It is truly fascinating to see the machines help keep us safe.
Modern defenses now rely on these intelligent algorithms to stay one step ahead of criminals. By using these advanced methods, businesses can focus on growth while their systems remain shielded. These updates ensure a brighter future for all users online.
The Evolution of Digital Defense Mechanisms
The landscape of cybersecurity is undergoing a significant transformation, driven by the integration of artificial intelligence and machine learning. As cyber threats become more sophisticated, traditional security measures are being augmented with advanced technologies to enhance threat detection and response.
“The traditional rule-based systems are no longer sufficient to protect against the evolving threat landscape,” notes a recent cybersecurity report. This limitation is driving the shift towards more proactive and intelligent defense mechanisms.
Moving Beyond Traditional Rule-Based Systems
Traditional rule-based systems rely on predefined rules to identify known threats. However, these systems are limited in their ability to detect unknown threats or zero-day attacks. Machine learning in cybersecurity is revolutionizing this landscape by enabling systems to learn from data and identify patterns that may indicate a potential threat.
By leveraging machine learning algorithms, cybersecurity systems can now analyze vast amounts of data to identify anomalies and predict potential threats. This proactive approach enables organizations to stay ahead of cyber adversaries.
The Shift Toward Proactive Threat Hunting
The integration of AI and machine learning is also driving a shift towards proactive threat hunting. Rather than simply responding to threats, organizations are now using advanced analytics and AI-driven tools to anticipate and prevent attacks.
AI threat detection is at the forefront of this shift, enabling organizations to identify potential threats before they materialize. By analyzing patterns and anomalies in real-time, AI-powered systems can alert security teams to potential threats, allowing them to take proactive measures to prevent attacks.
As noted by a cybersecurity expert, “The use of AI and machine learning in threat hunting represents a significant advancement in cybersecurity, enabling organizations to stay ahead of the threat curve.”
“The future of cybersecurity lies in the ability to anticipate and prevent threats, rather than simply responding to them.”
In conclusion, the evolution of digital defense mechanisms is being driven by the integration of AI and machine learning. By moving beyond traditional rule-based systems and adopting proactive threat hunting strategies, organizations can enhance their cybersecurity posture and stay ahead of emerging threats.
How AI Improves Cybersecurity Through Predictive Analytics
Predictive analytics, powered by AI, is transforming the cybersecurity landscape by providing proactive defense mechanisms against potential attacks. This transformation is largely due to AI’s ability to analyze vast amounts of data quickly and accurately, identifying patterns that may elude human analysts.
The core strength of AI in cybersecurity lies in its capacity to process and analyze massive data sets. This capability is crucial for identifying patterns that could indicate potential threats. By leveraging machine learning algorithms, AI systems can sift through enormous volumes of data, including network logs, user behavior, and threat intelligence feeds, to uncover subtle indicators of compromise.
Identifying Patterns in Massive Data Sets
AI’s pattern recognition capabilities are pivotal in enhancing cybersecurity. By analyzing historical data and real-time inputs, AI can:
- Detect anomalies in user behavior that may signal a security breach.
- Identify known threat patterns and predict the likelihood of their occurrence.
- Uncover hidden relationships between different data points that could indicate a sophisticated attack.
Anticipating Attacks Before They Execute
One of the most significant ai cyber security benefits is the ability to anticipate attacks before they happen. By analyzing trends and patterns, AI-powered predictive analytics can forecast potential threats, enabling organizations to take proactive measures to prevent attacks. This proactive approach is a significant advancement over traditional reactive cybersecurity strategies.
The integration of AI in cybersecurity through predictive analytics not only enhances the ability to detect threats but also automates the response, thereby improving ai security automation. This automation is critical in reducing the response time to security incidents, minimizing potential damage.
In conclusion, AI-driven predictive analytics is revolutionizing cybersecurity by providing organizations with the tools to anticipate and prepare for potential threats. By leveraging AI’s capabilities, businesses can significantly enhance their cybersecurity posture, staying ahead of the evolving threat landscape.
Automating Incident Response for Faster Mitigation
In the face of rising cyber threats, automating incident response is crucial for minimizing potential damage. As organizations increasingly rely on digital infrastructure, the need for swift and effective incident response mechanisms has become paramount. Artificial Intelligence (AI) plays a pivotal role in this domain by enhancing the speed and efficacy of responses to cybersecurity incidents.
Reducing Mean Time to Respond
One of the critical advantages of AI in incident response is its ability to reduce the mean time to respond to security incidents. Traditional manual processes can be time-consuming and prone to human error. AI-driven systems can analyze vast amounts of data quickly, identify potential threats, and initiate response protocols much faster than humanly possible.
- Rapid detection and analysis of security incidents
- Automated response to known threats
- Prioritization of incidents based on severity and impact
Orchestrating Security Operations Center Workflows
AI also significantly enhances the efficiency of Security Operations Centers (SOCs) by orchestrating workflows. By automating routine tasks and providing real-time insights, AI enables SOC teams to focus on more complex and high-priority tasks. This not only improves the overall response time but also enhances the effectiveness of the incident response.
- Automation of routine security tasks
- Real-time threat intelligence and analytics
- Enhanced collaboration among SOC teams through AI-driven insights
By leveraging AI for incident response, organizations can significantly mitigate the impact of cybersecurity threats. As cyberattacks continue to evolve, the integration of AI in incident response will remain a critical component of robust cybersecurity strategies.
Advanced AI Malware Detection and Behavioral Analysis
As cyber threats become more sophisticated, the role of AI in enhancing malware detection and understanding behavioral patterns is becoming increasingly critical. The traditional signature-based detection methods are no longer sufficient to combat the evolving landscape of cyber threats. AI-driven solutions are now being employed to detect and analyze malware more effectively.
Recognizing Zero-Day Threats
Zero-day threats are attacks that exploit previously unknown vulnerabilities in software or hardware. These threats are particularly dangerous because they can cause significant damage before a patch or solution is developed. AI-powered systems can recognize zero-day threats by analyzing patterns and anomalies in data that may indicate a potential threat. This proactive approach enables organizations to respond quickly to new threats.
AI algorithms can be trained on vast amounts of data to identify patterns that are indicative of malicious activity. By doing so, these systems can detect zero-day threats by recognizing unusual patterns that may not be caught by traditional security measures. The ability to detect unknown threats is a significant advantage in the cybersecurity landscape.

Analyzing Fileless Malware Techniques
Fileless malware is a type of cyber threat that does not rely on files to infect a system. Instead, it uses legitimate programs and tools already present on the computer to carry out malicious activities. AI-driven behavioral analysis is crucial in detecting fileless malware, as it monitors system and application behavior to identify potential threats.
By analyzing the behavior of applications and system processes, AI can identify when a legitimate tool is being used maliciously. This approach allows for the detection of fileless malware that traditional signature-based detection methods might miss.
The integration of AI in malware detection and behavioral analysis represents a significant advancement in cybersecurity. By leveraging AI’s capabilities, organizations can enhance their defenses against sophisticated cyber threats.
Strengthening Network Security with Machine Learning
As cyber threats evolve, machine learning emerges as a pivotal force in bolstering network security. By integrating machine learning into cybersecurity frameworks, organizations can significantly enhance their defense mechanisms against increasingly sophisticated threats.
Machine learning, a subset of AI, offers advanced capabilities for analyzing patterns and anomalies in network traffic, thereby improving incident response times and reducing false positives. This technology is crucial for enhancing cybersecurity through AI.
Monitoring Traffic Anomalies in Real Time
Real-time monitoring of network traffic is essential for identifying potential security breaches before they cause significant damage. Machine learning algorithms can analyze vast amounts of traffic data to detect anomalies that may indicate a cyber attack.
By leveraging machine learning for cybersecurity, organizations can automate the process of monitoring network traffic, reducing the reliance on manual inspection and improving response times. Advanced machine learning models can learn from historical data to recognize patterns associated with malicious activities.
Securing Distributed Cloud Environments
As organizations increasingly adopt cloud services, securing distributed cloud environments has become a critical challenge. Machine learning can play a vital role in this area by analyzing user behavior and network traffic to identify potential security risks.
By applying machine learning techniques, organizations can enhance the security of their cloud infrastructure. This involves using predictive analytics to anticipate and mitigate potential threats, ensuring the integrity and confidentiality of data stored in the cloud.

The Role of Artificial Intelligence in Identity Management
AI’s role in identity management is multifaceted, enhancing both security and user experience. Identity management is a critical component of cybersecurity, as it ensures that the right individuals have access to the right resources at the right time. With the integration of Artificial Intelligence, identity management systems are becoming more sophisticated, capable of adapting to the ever-evolving threat landscape.
The traditional identity management systems relied heavily on static passwords and simple authentication methods, which have proven to be inadequate against modern cyber threats. AI-driven identity management is changing this narrative by introducing advanced authentication protocols and anomaly detection mechanisms.
Adaptive Authentication Protocols
One of the significant advancements in AI-driven identity management is the implementation of adaptive authentication protocols. These protocols assess the risk associated with a login attempt based on various factors such as user behavior, location, and device information. By doing so, they can dynamically adjust the authentication requirements, making the process more secure and user-friendly.
For instance, if a user logs in from a familiar location, the system might only require a password. However, if the login attempt is made from an unfamiliar location or device, the system might prompt for additional verification steps, such as a one-time password sent to the user’s phone or a biometric scan.
Detecting Credential Stuffing and Account Takeovers
AI is also playing a crucial role in detecting and preventing credential stuffing and account takeovers. Credential stuffing involves attackers using automated tools to try stolen login credentials across multiple websites. AI-powered systems can identify such malicious activities by analyzing patterns of behavior that are indicative of credential stuffing, such as a large number of login attempts from a single IP address within a short timeframe.
Moreover, AI can help in detecting account takeovers by monitoring user behavior and flagging any unusual activity. For example, if a user’s account is accessed from a different country or if there are multiple failed login attempts followed by a successful login, the system can raise an alert, indicating a potential account takeover.
By leveraging AI in identity management, organizations can significantly enhance their cybersecurity posture. AI not only improves the security of identity management systems but also makes them more user-friendly by streamlining the authentication process and reducing the friction associated with traditional security measures.
Addressing the Human Element in Security
The human factor remains one of the most significant vulnerabilities in cybersecurity, and leveraging AI to mitigate this risk is gaining traction. Despite the advancements in cybersecurity technologies, human error and behavioral vulnerabilities continue to be exploited by attackers.
To combat these threats, organizations are turning to AI-driven solutions that can simulate real-world attacks and train employees to recognize and respond to them effectively. One such approach is AI-driven phishing simulation and training.
AI-Driven Phishing Simulation and Training
Phishing remains one of the most common attack vectors used by cybercriminals. AI-powered phishing simulation tools can create highly realistic phishing emails and training programs tailored to an organization’s specific needs. These tools analyze employee responses and provide targeted training to improve their ability to identify and report suspicious emails.
By leveraging machine learning algorithms, these simulations can adapt over time, becoming increasingly sophisticated to better prepare employees for the latest phishing tactics. This proactive approach not only enhances employee awareness but also significantly reduces the risk of successful phishing attacks.
Reducing Alert Fatigue for Security Analysts
Security teams are often overwhelmed by the sheer volume of alerts generated by security systems, leading to alert fatigue. AI can help mitigate this issue by analyzing alert data, identifying patterns, and prioritizing alerts based on their severity and relevance.
By automating the initial triage of security alerts, AI-powered systems can significantly reduce the workload on security analysts, allowing them to focus on the most critical threats. This not only improves response times but also enhances the overall effectiveness of the security team.
Implementing AI-driven solutions to address the human element in security is a crucial step towards strengthening an organization’s cybersecurity posture. By reducing vulnerabilities associated with human behavior and improving the efficiency of security operations, organizations can better protect themselves against the evolving landscape of cyber threats.
Navigating the Challenges of AI-Powered Security
While AI-powered security solutions offer enhanced protection, they also introduce complexities that need to be addressed. As organizations increasingly rely on AI in cybersecurity, it’s essential to understand the challenges associated with its implementation.
The Risk of Adversarial Machine Learning
One of the significant risks associated with machine learning in cybersecurity is adversarial machine learning. This involves attackers manipulating the machine learning models to evade detection or cause false positives. For instance, attackers might craft malware that is specifically designed to be misclassified by AI-powered security systems.
Adversarial machine learning poses a significant threat because it can compromise the effectiveness of AI-powered security solutions. To mitigate this risk, it’s crucial to develop and implement robust testing and validation procedures for AI models.
Balancing Privacy and Data Collection
Another challenge associated with AI-powered security is the need to balance privacy with data collection. AI systems require vast amounts of data to learn and improve, but this data often includes sensitive information. Organizations must navigate the complex landscape of data privacy regulations while collecting enough data to train their AI models effectively.
To address this challenge, organizations can implement data minimization techniques, ensuring that they collect only the data that is necessary for their AI systems. Additionally, they can use techniques like anonymization and pseudonymization to protect sensitive information.
- Implementing robust data governance policies
- Using data minimization techniques
- Employing anonymization and pseudonymization methods
FAQ
Q1: How exactly does ai in cybersecurity improve our defense against hackers?
A: AI in cybersecurity acts as a tireless digital guardian by processing data at a scale humans simply can’t match. By enhancing cybersecurity through ai, organizations can move from reactive measures to proactive defense. These AI-powered cybersecurity measures allow systems to spot suspicious activities the moment they occur, ensuring that your digital assets are protected around the clock.
Q2: What are the primary artificial intelligence cybersecurity benefits for modern businesses?
There are numerous artificial intelligence cybersecurity benefits, but the most impactful are speed and accuracy. Systems like CrowdStrike Falcon utilize AI to provide advanced threat detection with ai, significantly reducing the time it takes to identify a breach. Additionally, ai cybersecurity solutions help eliminate human error, which remains one of the leading causes of security vulnerabilities today.
Q3: How does machine learning in cybersecurity differ from traditional antivirus software?
Traditional software relies on “signatures” or a database of known threats, which means it often misses new attacks. In contrast, machine learning in cybersecurity identifies threats based on behavior. By using machine learning for cybersecurity, platforms like Palo Alto Networks can recognize anomalies in real-time, allowing for the detection of “zero-day” exploits that haven’t been seen before.
Q4: Can you explain how AI security automation helps IT teams?
A: AI security automation is a game-changer for overworked IT professionals. It handles the repetitive, high-volume tasks of triaging alerts, which helps in reducing alert fatigue for security analysts. By automating the initial incident response, tools like Microsoft Sentinel allow human experts to focus on complex strategy and deep forensic investigation rather than getting buried in “noise.”
Q5: How does AI malware detection handle fileless attacks?
A: AI malware detection is uniquely equipped to handle fileless attacks because it doesn’t just look for malicious files; it monitors behavioral patterns. By enhancing cybersecurity through ai, security protocols can detect when legitimate programs—like PowerShell—are being used for unauthorized activities, stopping the attack in its tracks before it can execute.
Q6: In what ways is ai in network security protecting cloud environments?
A: AI in network security is essential for managing the complexity of distributed cloud setups like those found in Google Cloud or AWS. It provides advanced threat detection with ai by constantly monitoring traffic patterns across various nodes. If a data packet looks out of place or an unauthorized user attempts to access a sensitive database, the AI triggers an immediate alert or lockdown.
Q7: What are the long-term impacts of ai on cybersecurity strategy?
The impacts of ai on cybersecurity are shifting the industry toward a “predictive” model. Instead of waiting for a firewall to be breached, ai threat detection uses predictive analytics to anticipate where a hacker might strike next. This shift makes ai-powered cybersecurity measures an indispensable part of any long-term risk management strategy.
Q8: How ai improves cybersecurity when it comes to phishing and social engineering?
A: How ai improves cybersecurity in the realm of phishing is quite fascinating. AI-driven platforms, such as those developed by Ironscales, analyze the linguistic patterns and metadata of incoming emails. They can spot subtle signs of spoofing that a human eye might miss, effectively blocking credential stuffing attempts and account takeovers before a user ever clicks a dangerous link.
Conclusion
In conclusion, the impact of AI on cybersecurity is multifaceted, offering advanced solutions to combat evolving cyber threats. Throughout this article, we’ve explored the various dimensions of AI’s role in enhancing cybersecurity, from predictive analytics and automated incident response to advanced malware detection and identity management.
AI’s ability to analyze vast datasets and identify patterns has significantly improved predictive analytics, allowing for the anticipation of potential threats before they materialize. Moreover, the automation of incident response has streamlined security operations, reducing the mean time to respond to threats.
The integration of AI in cybersecurity has also led to more sophisticated malware detection and behavioral analysis, capable of recognizing zero-day threats and fileless malware techniques. Furthermore, AI-driven identity management solutions have enhanced adaptive authentication protocols and detected credential stuffing and account takeovers.
As we’ve seen, AI is not just a tool but a strategic asset in the cybersecurity arsenal, enabling organizations to stay ahead of cyber adversaries. By embracing AI-powered security solutions, businesses can significantly bolster their defenses against the increasingly complex cyber threat landscape.
In summary, the fusion of AI and cybersecurity is a powerful synergy that is rapidly strengthening our digital defenses. As cyber threats continue to evolve, the role of AI in cybersecurity will only continue to grow in importance.
About the Author & Disclosures
John Cosstick is Founder-Editor of TechLifeFuture.com and winner of the 2024 BOLD Award for Open Innovation in Digital Industries. He is a former banker, accountant, and certified financial planner.
He is now a freelance journalist and author. John is a member of the Media Entertainment and Arts Alliance (Union). You can visit his Amazon author page by clicking HERE.
Authority Reference Links:
For those interested in delving deeper into the world of AI cybersecurity solutions, several key resources are available. The following links provide additional insights and information on enhancing cybersecurity through AI.
The references listed below are categorized for ease of access and understanding:
- AI Cybersecurity Solutions
- Enhancing Cybersecurity Through AI
- Predictive Analytics in Cybersecurity
- AI-Driven Incident Response
These resources offer a wealth of information on the latest developments and strategies in AI-powered cybersecurity. By exploring these links, readers can gain a more comprehensive understanding of the topic.
Further reading on AI cybersecurity solutions and enhancing cybersecurity through AI can provide valuable insights into the future of digital defense mechanisms.
👉 https://www.ibm.com/think/x-force/2025-cost-of-a-data-breach-navigating-ai
👉 https://newsroom.ibm.com/2024-07-30-ibm-report-escalating-data-breach-disruption-pushes-costs-to-new-highs
👉 https://www.allaboutai.com/resources/ai-statistics/cybersecurity/
👉 https://www.lakera.ai/blog/ai-security-trends
👉 https://www.totalassure.com/blog/ai-cybersecurity-stats-2025
👉 https://thenetworkinstallers.com/blog/ai-cyber-threat-statistics/
👉 https://www.sentinelone.com/cybersecurity-101/cybersecurity/cyber-security-statistics/
👉 https://deepstrike.io/blog/ai-cybersecurity-threats-2025
👉 https://www.weforum.org/stories/2024/02/what-does-2024-have-in-store-for-the-world-of-cybersecurity/
👉 https://www.nist.gov/cyberframework